According to a new IDC report, there will be 41.6 billion IoT devices by 2025, and they will be generating 79.4 zettabytes of data. Connected devices communicate with each other, transfer datasets, and work within a single ecosystem. To do this efficiently, they need to be updated regularly, like laptops and mobile phones.
However, an update of embedded systems that give voice to smart devices is not limited to overwriting files with new copies. It is a complex end-to-end mechanism, which must be both consistent and seamless: users don’t want to be directly involved in the process of patching, fixing, and enhancing their device.
Over-the-air (OTA) updates enable efficient and remote operations. But there is a new set of challenges to consider.
What is an OTA update?
As described by Gartner, OTA refers to the ability to download applications, services, and configurations over a mobile or cellular network. It happens “over-the-air”, i.e., there’s no need to connect a given device to another device to install the updates.
In embedded development, an OTA mechanism implies regular updating of Internet-connected hardware with new settings, software, and/or firmware via Wi-Fi, mobile broadband, and built-in functions in the device OS.
OTA mechanisms play an integral role in Internet of Things application development and include:
- Firmware over-the-air (FOTA) updates. The technique is used in hardware components, like Electronic Control Units (ECUs) of ADAS systems in the automotive industry. For instance, Tesla uses new fixes and features, like an advanced autopilot, in its cars in the field via FOTA updates.
- Software over-the-air (SOTA) updates. These include security patches, software updates, and new functionality implementation: updated navigation maps and infotainment screens in smart cars; smart metering and smart heating in connected homes, etc.
Benefits of OTA Updates in IoT
- Improved safety and compliance. OTA mechanisms allow developers to patch known vulnerabilities over the air, instead of recalling devices. Also, they ensure compliance with the evolving legal and regulatory responsibilities faster and more cost-effectively.
- Maintenance cost reduction. When fleets of devices are deployed in the field, it is impossible to ensure regular manual updates. OTA systems enable seamless updates from a single unified interface as an alternative to costly and time-consuming field services.
- Continuous improvement. OTA updates allow manufacturers to continuously amend their connected systems, fix bugs, and enhance product performance, even when they are on the production line or in the hands of a consumer. This approach eliminates recalls and in-person maintenance and provides a competitive edge: this way, there is no need to wait to incorporate new features in a new batch of devices.
- Additional revenue streams. Original Equipment Manufacturers (OEMs) can implement add-ons through OTA updates after the release, without physical access to the firmware that needs an upgrade.
- Decreased operations costs. According to the Stout Risius Ross report, software issues account for 15% of the all-industry recalls. OTA technology streamlines software upgrades and fixes, and, as projected by IHS Automotive, is capable of saving businesses over $35 billion in operational costs.
Current Challenges facing OTA Mechanisms
If OTA updates improve connected devices, why do we so often hear horror stories about bricked, i.e. non-functioning, devices, people stuck in their apartments because of smart lock glitches, and hijacked car alarms?
- Context-awareness. With certain devices, like connected cars or tools used for medical means, any modification poses a degree of risk. This happens when a system sends updates while a device is performing a critical task.
- No rollback to an earlier version. One of the most famous scandals associated with a failed OTA mechanism happened in 2017. Airbnb deployed a corrupt software update to the incorrect devices — a previous version of the smart lock, used in the company’s rental properties. The devices got bricked and were unable to receive another OTA update to fix the issue. The system’s functionality didn’t include an automatic rollback, which made it impossible for renters to enter their apartments. As a result of the mishap, the locks had to be manually updated by the vendor.
- Security issues. The list of potential vulnerabilities in OTA systems is huge: Man-in-the-Middle (MITM) attacks, introduction of malware, and other weak points. This happens due to unprotected transfer channels for critical data, lack of digital signatures or code signing, absence of update authentication, and so on. As a result, hackers can modify a valid update, inject malicious code, take over a device, and reprogram sensitive components of the embedded system.
- Scalability. With the growing number of connected devices, OTA systems must be capable of adapting to ever growing needs and informing hundreds to thousands to millions of devices. Developers should allow administrators to schedule updates to their devices to avoid network saturation and limit unintended downtime. Another challenge is to ensure a built-in support of configuration options for automatic updates, adapted to bandwidth constraints.
How to Approach OTA Technology Implementation: 3 Strategies
The chosen implementation strategy should be aligned with the nature of the IoT devices in question, the system’s architecture, and the available technological choices.
A product owner chooses between building a custom OTA system from scratch and purchasing a ready-to-use OTA solution from a vendor.
The former approach provides more freedom and control over remote updates, while the latter accelerates time-to-market and comes as a more cost-effective solution.
If a product owner opts for a custom OTA solution, there are three major frameworks to bring the project to life:
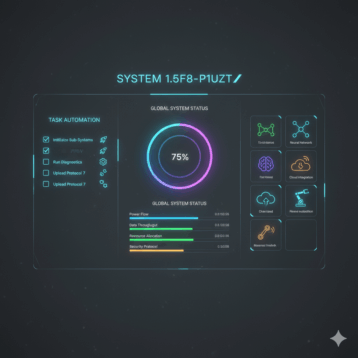
- Edge-to-cloud OTA updates. A connected device with a built-in microcontroller receives OTA packages from a remote server. The package can include upgrades to both the microcontroller’s underlying hardware capabilities (FOTA) and updates to applications running on them (SOTA).
- Gateway-to-cloud OTA updates. A system featuring an Internet-connected gateway (for instance, a telematics system), which manages a set of local devices, and receives updates from a remote cloud-based server. The updates include newer versions of the installed software applications, the app’s host environment, and/or the gateway device’s firmware.
- Edge-to-gateway-to-cloud OTA updates. An Internet-connected gateway acts as a dispatcher, downloads updates from the cloud-based server, and then dispatches to another edge/gateway.
OTA Updates Best Practices
- Focus on an OTA mechanism from day one. Product owners and development teams tend to neglect the development, testing, and effective implementation of OTA update capabilities. As a consequence, OTA mechanisms are being assembled hastily and lack many basic requirements. In a worst-case scenario, OEMs avoid additional hardware costs and don’t include the mechanism into the IoT development lifecycle at all.
- Check the developers’ competency in building secure and reliable OTA mechanisms. A vendor’s IoT expertise doesn’t guarantee the capability to roll out fleet wide updates. Developers with prominent skills in IoT systems may not have any experience in establishing a fail-safe update system.
- Adopt a progressive deployment approach. Administrators should be free to schedule updates to their devices to avoid network congestion, overstressing, and denial-of-service (DoS) issues. A progressive deployment approach will ensure that sets of IoT devices are updated before rolling out a massive batch.
- Consider criticality-of-use issues when scheduling specific updates. For example, there should not be updates when a connected car is being driven or when medical devices are being used.
- Ensure atomic updates with built-in rollback. A faulty update caused by power loss or a network issue can brick a device, and it will demand a complete recovery. However, if it is accomplished atomically, i.e., with a rollback to the last functioning version, an unexpected event won’t lead to device bricking. Also, it would be worthwhile to store basic IoT properties, such as hostname, networking configuration, and key features configuration, in a specific file that can be read by any version of an upcoming update.
- Integrate backup services into the current working configuration. If an issue occurs during the update process, an IoT device will reload the last known and trusted configuration, which is stored on an upstream repository hosted by a private or public cloud platform. This feature is supported by major cloud providers: Amazon Web Services (AWS) IoT service supports Thing Shadows, while the Microsoft Azure IoT Hub supports device twins.
- Build a management server. A management server will store inventory lists and keep track of the running software and firmware versions. Basic IoT properties — e.g., hostname, networking configuration, and features configuration — should be stored in a specific file that can be read by any version of the firmware.
- Security. The three main challenges, concerning the safety of the transmitted data over the air, include:
- Authentication: data must be sent from a trusted server to the client
- Confidentiality: access to in-transit data must be granted to a predetermined number of users
- Integrity: transmitted updates should not be corrupted.
One security technique is data origin authentication (DOA). With DOA, each update is digitally signed by the vendor, and the digital signature must be verified by the IoT device before starting the update.
Conclusion
With OTA updates, there isn’t a one-size-fits-all solution, as every IoT system has its own set of requirements and constraints. A skillful team will tune an OTA system to address them and deliver an effective OTA solution.