Today, organizations have access to vast amounts of data, which is vital for their growth. Therefore, it is essential to have a scalable and cost-effective method of handling and securing data. This is why most companies are shifting to cloud security. In fact, it’s projected that in 2020, enterprises will have 83% of their workloads in the cloud.
However, there are still significant concerns among IT professionals regarding security in regards to cloud computing. Though the concerns are understandable, they stem from the fact that organizations are yet to understand cloud computing well, and how it differs from traditional IT security.
To know which security approach is suitable for your organization, you must first understand how they resemble and differ from each other.
Traditional IT Security
Businesses have relied on traditional IT frameworks to collect, store, and process data for many years. With this approach, your organization purchases, hosts, and maintains the servers you use for data collection, storage, and processing.
As such, it has a high initial cost of setting up, but it gives you control of your security plan. The security devices you purchase, network control management, and your response to threats is all up to you.
With this approach to IT security, you can monitor data and know where and how it’s being controlled daily. However, as your data needs increase, you will require additional hardware with more computing power.
You will also need to add more personnel to your IT team to manage the hardware. As such, with the added infrastructure and personnel needs, scaling your data processing capacity is expensive.
Cloud Security
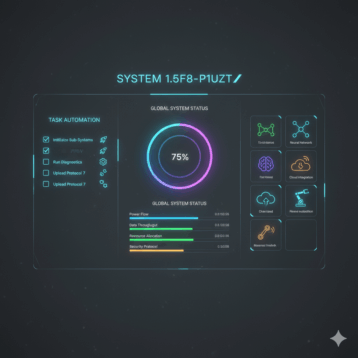
Unlike traditional IT systems, cloud computing security employs an Infrastructure-as-a-Service approach. This means that you can access as much infrastructure as you need from a third party (cloud provider).
Though you will lose control of some aspects of data security, cloud computing makes data security management more manageable. This is because, by working with a reputable cloud services provider, you eliminate the hassle of managing and maintaining hardware. More importantly, they have personnel who are specialized in matters of data storage and security.
With cloud security, you can take one of three approaches.
1. Public Cloud
The public cloud is an IT security approach that involves getting computing services from third-party providers via the internet. Some of the most popular public cloud service providers are Amazon Web Services (AWS), Google Cloud, and Microsoft Azure.
Public clouds facilitate resource sharing and enable businesses to scale their data processing capabilities. Though services vary from one provider to the next you will benefit from:
- Software
- Storage Space
- Virtual machines
Once you set up your account, all you need to do is select the services your business needs. Though some may be offered for free, others are sold on-demand. This means you will only be charged when you use the service.
With public clouds, your business can adjust data processing capacities according to the demand. This saves you any unnecessary computing costs while ensuring your company can deliver value to your customers.
However, you must work with your cloud provider to ensure that data security frameworks are effective. This is because public clouds are a primary target for hackers as they host a lot of sensitive data.
2. Private Cloud
If you’re worried about the security risks that come with public clouds, you may opt to set up a private cloud for your organization. With this approach, you will be responsible for setting up security protocols and data management. All your infrastructure, data, and software will be accessible remotely.
On the other hand, you will have to set up a data center and have a team to manage your infrastructure, which will be very expensive.
3. Hybrid
A hybrid cloud is a cloud computing approach that involves the use of both public and private clouds. This approach allows your organization to use the well-established software and infrastructure of public clouds while storing sensitive data in a private cloud.
Private clouds are perfect for storing data such as:
- Social Security Numbers
- Payment information
- Addresses
With a hybrid cloud, your organization will get the best of cloud computing. The Platform-as-a-Service element from your public cloud provider gives you the flexibility to scale as and when needed cost-effectively. On the other hand, your private cloud ensures that your most sensitive data well-secured.
Here are some steps you should take to mitigate security threats when using a hybrid cloud:
- Review all the data stored in the cloud regularly
- Have a vendor management system in place
- Understand all your compliance requirements
- Know your vendor’s controls
All these measures should be topped off by a continuous assessment of threats as they are evolving.
The Future Data Processing
Cost management and efficiency are critical ingredients in the growth of a company. Without a doubt, cloud computing is the future of data processing as it offers organizations greater security and flexibility at manageable costs.