API stands for application programming interface. An API is a software intermediary that allows two different applications to talk to each other. Every time you use an app such as Facebook, you send an instant message or look at the weather forecast on your phone, you are using an API.
APIs are the most common communication channels for internet traffic. Making them secure is becoming ever more important – and more challenging. APIs are so prevalent that they massively widen the attack surface of organizations. APIs are a huge security threat.
Cloud Security
It can be argued that nobody really cared about cloud security until most organizations started migrating everything onto the cloud. The number of APIs being developed and put into use has exploded.
In the past, APIs were not as common. Perhaps they were used for mobile apps or B2B traffic. Now, almost everything is powered by an API. All of these new APIs introduce a lot of new risks when it comes to security and compliance.
API Security Risks
API security risks can be put into two very broad categories. The first is technical vulnerabilities. This includes a ton of risks that can exist in all standard web applications. This includes the OWASP top ten web application security risks, as well as CVE vulnerabilities. The Log4j vulnerability can be included in this category. This shows that these security flaws can be far reaching.
These technical vulnerabilities can be the most acute security risks. Usually, they simply require adopting the existing app security strategies. This can include code scanning during the API development process. It can also involve deploying firewalls or runtime app self-protection technology. These are pretty easy to implement.
The second big security risk is more unique to the world of APIs. APIs are different from older web applications. API security is fundamentally a problem with data security.
APIs allow for the quick access of data by systems or people. This can include modulating the data. Many strategies in API security have been adopted from data security. Organizations need to understand who is accessing the data, where sensitive data is being stored, and which APIs may be exposing sensitive data.
Steps Towards API Security
The first step towards API security is discovery and knowledge. This means building an API inventory.
As you get deeper into this process, you need to determine what kind of data is being processed by each API. This will allow a company to understand their risk profile. They can chart the risk profile across all API endpoints. The API endpoint is the point at which the API connects with the software program.
The second step of API security involves monitoring APIs. What is the structure of the API? What API requests are coming into the system? Who is accessing these, and do they need security classification levels? Companies need to monitor API traffic and look out for any activity that could be malicious.
The third step involves protection. This can include threats that need to be blocked in real time. These kinds of security attacks can ruin an entire company with just one malicious request. Log4j is a good example of this kind of threat that needs to be dealt with in real time.
Other attackers will play a long game. This requires looking at a whole chain of events rather than at just one API request. It means needing to understand and be able to profile how APIs and data are being accessed by customers and clients over a longer period of time. These kinds of attacks will likely be coming from bots.
The fourth stage of API security involves verification and compliance. Organizations need to set guardrails around what their teams will be doing. They should be proactively testing APIs early so that any potential issues can be identified and dealt with.
Using Technology
Most companies who are using a web application will already have a Web Application Firewall (WAF). As organizations expand their use of different apps, a standard WAF will not provide enough security.
API-driven applications have their own security vulnerabilities. They require more than the standard web security approach. Using a firewall to protect your APIs can be equated with bringing a knife to a gunfight.
API security solutions look at the way that applications behave on a day-to-day basis. These security solutions are powered by machine learning. They will learn the usual behavior of the application and bring any anomalies to the surface.
Any tiny deviations in user interaction may indicate a cyber attacker who is probing the application for flaws or trying to exploit an API vulnerability.
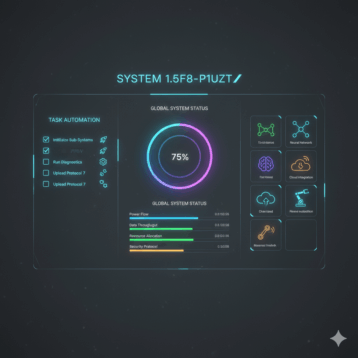
Any API security solution should fit the following criteria:
- It will identify all APIs within the organization. The security tool should know the parameters defining API requests that are permitted.
- The security tool should learn API behavior based on traffic driven by users. This allows the tool to learn every nuance that will define the normal behavior of the application. Any deviations will be highlighted.
- A good API security tool will be adaptable. Modern applications are constantly being updated and modified. The security tool should be able to accommodate these kinds of changes.
Analyzing Threats
Cybercriminals will wage sophisticated campaigns that are well planned. They will take all necessary precautions to avoid detection. To fight them, strong threat analysis is needed. The volume and quality of data provided by your API security tool is vital.
Data needs to be collected from all interaction points. The more data that is collected, the easier it will be to separate legitimate user interactions from malicious cyber threats.
In Summary
APIs are very vulnerable to attacks from cybercriminals. Firewalls are not effective in protecting API-driven applications. API security utilizes machine learning and is more sophisticated than previous security solutions.
When choosing an API security tool, ask yourself some simple questions. How does the tool deliver visibility? How well does the tool understand the applications I use? What is the quality and depth of the data collected by this security tool?
You certainly need tools that are designed especially for API security. This will protect you from cyber attacks that are designed to exploit your data.