The world is getting “smarter” by the minute. We live in smart homes, work in smart offices, drive smart cars and of course, use smart phones. A programming novice can now build a whole website using smart apps. The average employee can setup and manage their own devices at work.
The fundamental way in which we interact with technology, both in our personal and professional lives, has transformed. Just five years ago, the thought of operating a company without an in-house IT team was unthinkable. Today, SaaS and PaaS technologies have enabled businesses to set up and run their operations successfully without expert help. The reliable “IT guy” of yesteryears is suddenly in danger of becoming extinct.
Or is he?
Here are a few “survival tips” from Power Consulting Managed IT Services that smart CIOs and tech leaders can use to retrain, reengage and refocus their teams towards nourishing and improving business operations on the back of evolving technology.
Embrace the Cloud
Since its emergence over a decade ago, cloud computing has replaced on site software and infrastructure applications at a blistering pace. The cloud computing market will hit $186 billion by the end of 2018, and is all set to exceed $300 billion in market size by 2021. This shift of software, development platforms and IT infrastructure from on premise to the cloud is inexorable and is a reality that IT teams need to embrace, sooner rather than later.
Spend time on researching the most important features of the leading cloud service providers. Understand how well they will
- Integrate with your existing technologies
- Fulfill all the requirements your end-users need to manage their workflows efficiently
- Ensure your data and processes are secure and actively prevent malicious attacks
- Scale and expand their scope as your business operations grow
Cloud solutions work on a subscription model and come in three types:
- Infrastructure as a Service (IaaS): Preconfigured hardware and software delivered through a virtual interface. For example, web hosting with Amazon EC2.
- Platform as a Service (PaaS): A UI with operating system or system libraries in addition to infrastructure. For example, application building with Google App Engine.
- Software as a Service (SaaS): Fully functional web-based applications with features available on demand. For example, customer relationship management with Salesforce
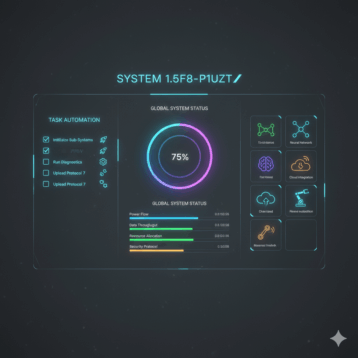
The last solution – SaaS – is easily the most popular solution in use today. It has enabled automation of the most time and resource-intensive tasks, which earlier needed to be carried out by multiple instances of software installed across numerous desktop and laptop computers.
Take information systems management, for example. Not many years ago, IT managers in the enterprise used to spend hours every month installing or updating software, scanning for viruses or rogue devices, managing users and permissions, and more. A cloud-based software and security management platform such as Cloud Management Suite offers rapid scalability and remote accessibility in tracking and managing multiple devices in your network. CMS does away with the need for having servers or agents to maintain and deploy software. This lets you get work done with less powerful systems, reduces downtime, minimizes manual intervention, and mitigates security threats in real-time.
Clear BYOD and IoT Strategies
Today’s corporate network is populated not just with company-issued devices, but with a range of different devices owned and managed by employees themselves. From laptops to smartphones to wearables, the variety of devices in a BYOD (Bring Your Own Device) setup can be extensive. BYOD policies not only give employees flexibility to use their devices, it puts them at ease with using familiar devices for work processes.
Many organizations look to BYOD as a way of cutting costs of purchase while still keeping efficiency high. Then there are the smart devices that make modern offices function smoothly, like smart lights, smart thermostats, smart security devices, and more that rely on monitoring users and their activities closely to complete their tasks. Some even use sensitive user information like fingerprints or other biometric identifiers that place the onus of securing this data on the organization.
With personal devices doubling up as work machines, the security risks that come with them are much higher. It can become difficult to monitor and control the various apps and software a user might download on their device that might pose a threat to your workflows and privileged data. These risks notwithstanding, it is essential to remember that employees are your partners and are equally invested in the company’s growth. Treat them with that basic respect when crafting policies aimed at mitigating and managing IT risks to the company. The IT team in such environments is burdened with treading a fine line between device security, workflow efficiency and respecting employee privacy.
While requiring your employees to set non-hackable passwords, use two-factor authentication, VPN tokens and secure networks only on their BYOD devices is acceptable, taking over device management into the hands of your team might be crossing the line. Require users to install lost device management software and the standard security apps that you would on company owned devices. Training employees on the various ways their BYOD devices can be attacked by hackers and how-tos to avoid security breaches is another must in BYOD setups.
From “Gatekeeper” to “Facilitator” to “Partner”
In the traditional scheme of things, the IT department fulfilled and managed all software and hardware needs of employees in an organization. No device came in without their stamp of approval, no software was considered without their recommendation and blessing. Any infringement of IT policies was met with swift and sure action – taking away user privileges, limiting access and so on.
As technology has become more accessible, employees have embraced its role in every aspect of their lives. They’ve gone from viewing the IT department as a “controlling” force to being a supportive, helping hand. The ease of use of newer technologies means, often, adventurous users leave caution to the winds and explore (and install!) tools that the IT department has no clue about.
Add to this unsupervised experimentation, the trend of automation in every aspect of work. From data modelling and business intelligence tools for your analytics team to product recommendation engines, product information management and order processing systems for your e-commerce team to social media management platforms, marketing automation and CRM tools for your marketing team; the list of tools that manage automated workflows grows every day.
Make it your job to stay informed and share that knowledge with your employees. Keep up with the technologies and trends that matter to your organization. Proactively share information that will help specific teams on a regular basis. Reach out to different teams on a regular basis to understand where they stand from a technology perspective, how well equipped they are with their current tools and platforms and what gaps exist. When employees view you as a reliable resource for everything technology-related, they’ll turn to you for guidance and help of their own accord.
Change is Good
The only constant in the tech landscape is change. As the custodian of the company’s technology stack, your role is to stay one step ahead of these changes at all times. Remember, not only are you the navigator for your organization through the challenging seas of the changing tech landscape, you’re also their defender against unforeseen security and privacy threats. Even regulatory changes like the EU’s GDPR, which may seem hard to meet at the outset, are a positive step forward in gathering accurate data and analytics with the full permission and trust of your customers.
Time to suit up, buckle down and charge your team into to a brave new tech world. Onward, Captain!