The rapid growth of the digital economy has created a wealth of opportunities for the media and entertainment industry. Content creators benefit from easier access to distribution, allowing them to reach global audiences much more easily than was previously possible. On the flip side, the proliferation of digital devices and streaming access has created an on-demand culture where consumers dictate what content they want to watch, when they watch it, and how they watch it.
With SCIM, when someone new is added to a system, they’re automatically set up in different apps and programs without needing to do it manually, whether on-prem or cloud.
But with opportunity comes risk.
The disruption caused by digitalization in the media and entertainment sector has ushered in a new era of cybercrime. The 2014 hack of Sony, which leaked sensitive information about its network architecture as well as personal employee documents, resulted in more than $15 million in investigative and remediation costs. And last year, three of the biggest brands in Hollywood –– Disney, Netflix, and HBO –– suffered intellectual property theft at the hands of hackers.
This is not to say that technology is to blame for these unfortunate occurrences (after all, content piracy has been going on for many decades). It does, however, stress the importance of digital governance and data protection. And this is where cloud computing comes into play.
Given the explosive growth of digital content, more and more businesses are migrating to the cloud to manage increasingly complex content management and distribution processes. Aside from cost savings and flexibility, one of the key benefits of operating in a cloud environment is cutting edge security. For many organizations, resources are limited –– IT departments are spread thin or there is not enough bandwidth to continuously manage product improvements. With cloud-based technologies, trained experts are able to handle security measures day in and day out.
Let’s take a look at some of the common security offerings of cloud-based content management systems.
1. Regulatory compliance
Top cloud computing security solutions within the media and entertainment space are typically SOC 1 & SOC 2 certified. These certifications are key because there is a huge distinction between the security of the cloud and the security of the data you put into the cloud. Auditors for the SOC frameworks periodically check the security, accessibility, and data protection of cloud vendors to verify the effectiveness of service to their clients.
2. Data encryption
Rights management technologies typically employ data encryption mechanisms to ensure that sensitive information is never compromised –– whether that be by hackers or anyone not authorized to view data. A reliable vendor should be able to claim that they encrypt data and regularly change their encryption keys.
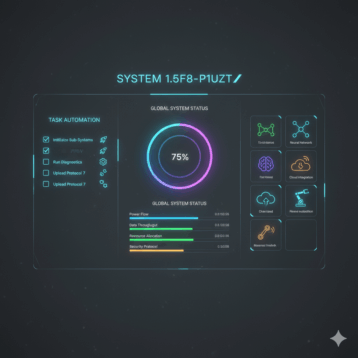
3. Access control
The biggest culprit in data breaches is often the result of employee negligence. Major cloud vendors help to combat this problem by offering identity and access control tools so that internal and external stakeholders always know who has access to what data and when.
4. Patch management & deployment
Most successful computer attacks exploit well-known vulnerabilities. Fortunately, security patches exist to ensure software systems are up-to-date. The problem, however, is that many organizations don’t always have the ability to adequately and consistently perform and test these time-consuming tasks. Cloud providers take on this added responsibility to ensure that software systems are never left in a vulnerable state.